Importance of Multi-Factor Authentication (MFA)
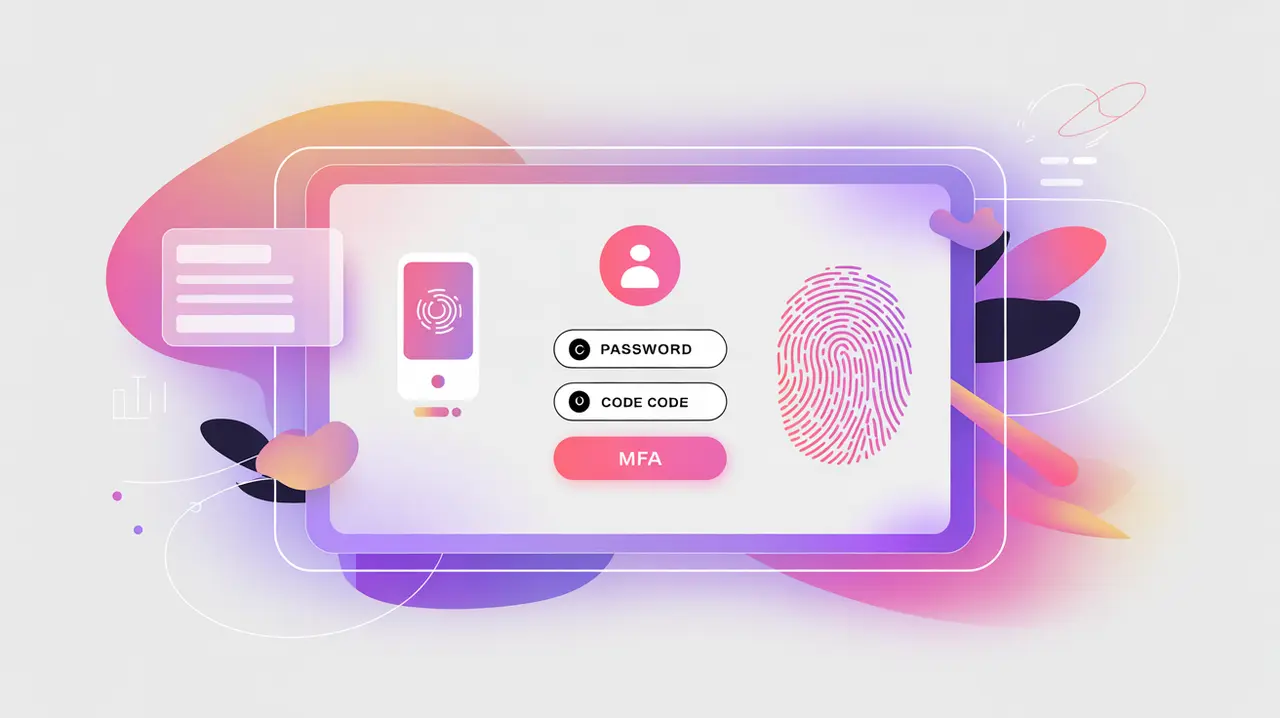
Multi-Factor Authentication (MFA) is a security method that requires users to provide two or more forms of verification before gaining access to a system. These factors generally fall into three categories: something you know (a password), something you have (a device or token), and something you are (biometrics). Its importance today lies in the rising frequency of cyberattacks and credential theft, where relying on passwords alone is no longer sufficient. MFA adds layers of defense that significantly reduce the risk of unauthorized access.
For social innovation and international development, MFA matters because mission-driven organizations often manage sensitive health, education, and financial data. By ensuring that access depends on multiple verification steps, MFA helps protect vulnerable communities and builds trust in digital platforms used across diverse and resource-constrained environments.
Definition and Key Features
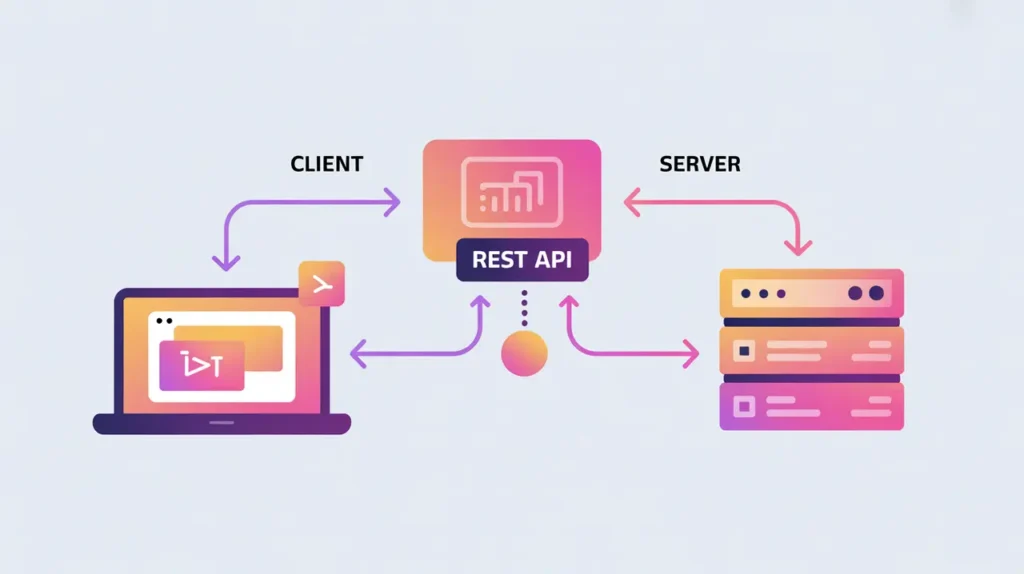
MFA works by combining independent factors so that even if one is compromised, an attacker cannot easily gain access. Examples include entering a password followed by a one-time code sent to a mobile device, or logging in with credentials and then confirming identity with a fingerprint scan. Cloud platforms, enterprise systems, and mobile apps increasingly support MFA as a baseline security measure.
MFA is not the same as two-step verification, which often relies on a single factor presented twice (such as a password and a recovery email). Nor is it equivalent to password strength requirements, which improve security but remain vulnerable to phishing or brute-force attacks. MFA represents a fundamental shift toward layered, resilient security.
How this Works in Practice
In practice, MFA can be implemented with SMS codes, mobile authenticator apps, physical security keys, or biometric methods. Security keys using standards like FIDO2 offer the strongest protection, while authenticator apps are considered more secure than SMS, which can be vulnerable to interception. Organizations must balance security with usability, ensuring that MFA methods remain accessible to all users, including those in low-connectivity regions.
Challenges include managing usability trade-offs, avoiding exclusion of users without smartphones or biometric devices, and addressing “MFA fatigue,” where users become careless about repeated prompts. Successful MFA deployment involves offering multiple verification options, providing fallback methods, and educating users about best practices.
Implications for Social Innovators
MFA strengthens the resilience of mission-driven digital systems. Health initiatives use it to safeguard access to electronic health records. Education platforms apply MFA to protect student data and staff portals. Humanitarian agencies require MFA for field staff accessing sensitive crisis-response systems from high-risk environments. Civil society groups adopt MFA to secure communications, donor platforms, and advocacy data against intrusion.
By layering security factors, MFA reduces vulnerabilities and ensures that critical services remain trustworthy and resilient, even in contexts where risks are heightened.