Importance of Encryption at Rest and In Transit
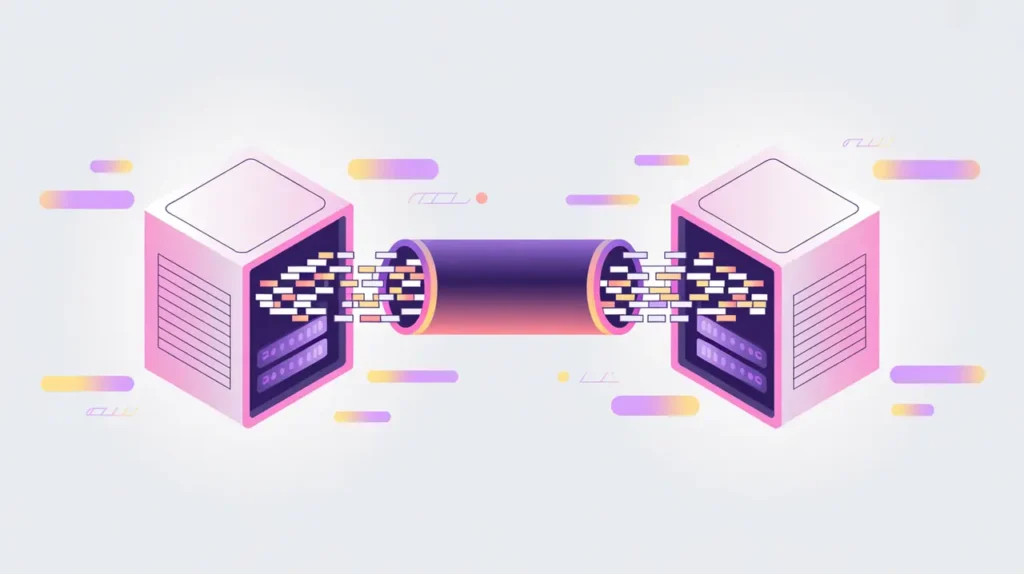
Encryption at Rest and In Transit are security practices that protect data when it is stored and when it moves across networks. Encryption at Rest secures data in databases, storage systems, or devices so that even if physical media is compromised, the data remains unreadable. Encryption in Transit protects data as it travels between systems, such as from a user’s device to a server, preventing interception or tampering. Their importance today lies in the growing reliance on cloud services and AI-driven applications that process sensitive personal and organizational data.
For social innovation and international development, encryption at rest and in transit matter because organizations frequently handle health records, educational outcomes, financial data, and crisis reports. These practices ensure that sensitive information remains protected, helping to maintain trust and comply with international privacy and security standards.
Definition and Key Features
Encryption at Rest typically uses algorithms like AES (Advanced Encryption Standard) to secure data on disks, databases, or object stores. Keys are required to decrypt the data, often managed by key management systems. Encryption in Transit commonly uses protocols such as TLS (Transport Layer Security) to establish secure connections between clients and servers. Together, these practices provide end-to-end protection for sensitive information.
They are not the same as anonymization or tokenization, which transform data to protect privacy but do not secure it directly. Nor are they equivalent to access control, which governs who can interact with data. Encryption specifically ensures that even if data is accessed without authorization, it cannot be understood or misused.
How this Works in Practice
In practice, enabling encryption at rest often involves configuring storage systems, databases, or cloud services to automatically encrypt all data. For encryption in transit, TLS certificates and secure communication protocols are implemented to ensure confidentiality and integrity. Many modern platforms make these defaults, but organizations must still manage keys, renew certificates, and audit configurations.
Challenges include performance trade-offs, key lifecycle management, and ensuring interoperability across systems. Misconfigurations, such as failing to enforce TLS or storing unencrypted backups, can leave critical gaps. Robust governance and automation are necessary to maintain effective encryption practices at scale.
Implications for Social Innovators
Encryption at Rest and In Transit are essential safeguards for mission-driven organizations. Health programs rely on them to protect electronic health records stored in the cloud and transmitted across hospital networks. Education platforms secure student data during online assessments and while archived in digital repositories. Humanitarian agencies encrypt crisis response data so that reports and communications remain confidential even if networks are insecure. Civil society groups use encryption to shield advocacy data from interception or misuse.
By protecting data wherever it resides or travels, encryption at rest and in transit strengthen trust and resilience, ensuring sensitive information remains safe in mission-critical environments.